Resource Center: Containers & Cloud Native Security
eBooks, Product Sheets, Whitepapers, Webinars and Videos
Filter Resources
Topics
- All
- KSPM 3
- Kubernetes Security 3
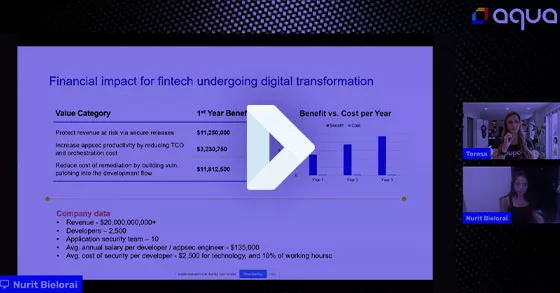
- Financial Services 8
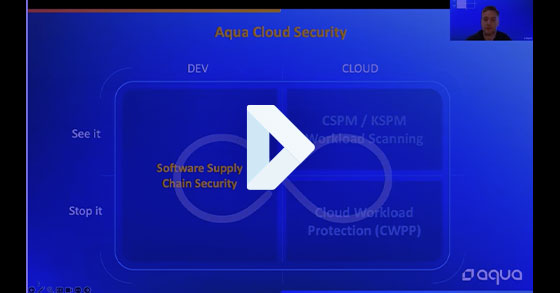
- CWPP 14
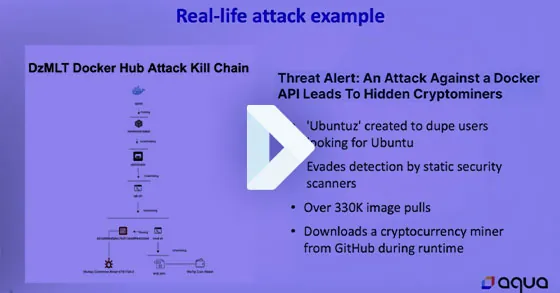
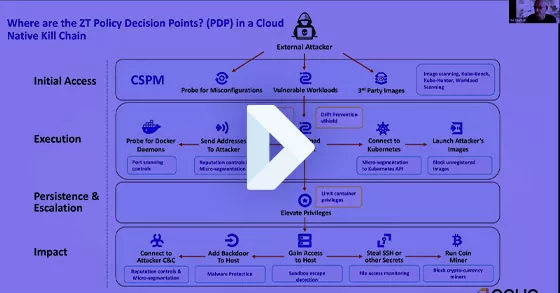
- cloud attacks 2
- Federal cloud native security 9
- Software supply chain security 19
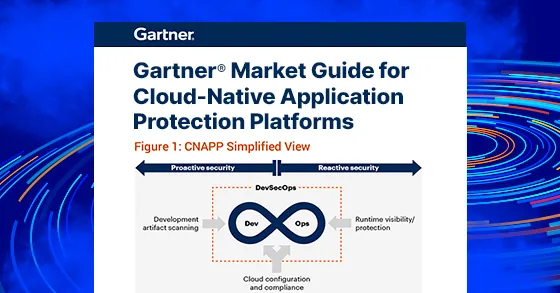
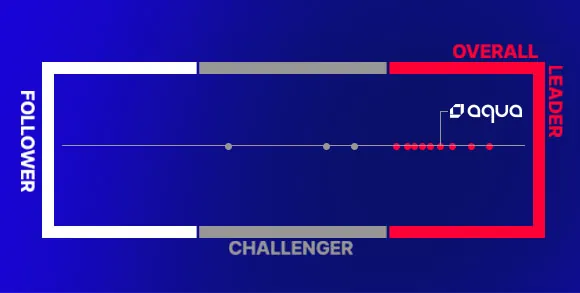
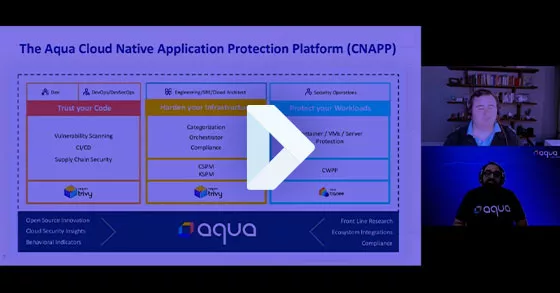
- CNAPP 30
- Container Security 66
- AWS Security 28
- Azure Security 8
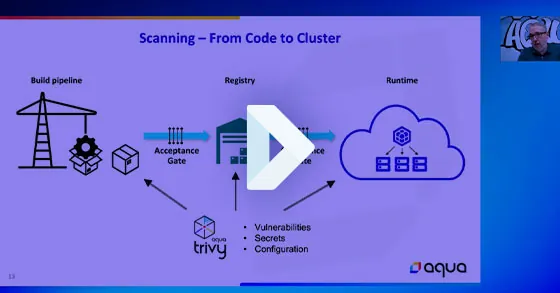
- CI/CD 10
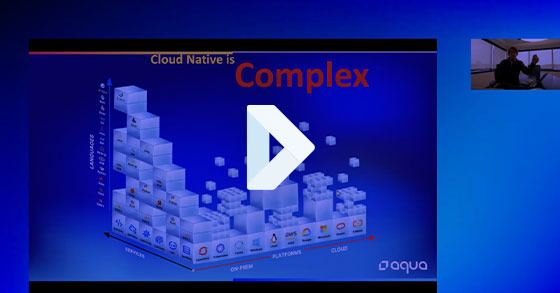
- Cloud Native Security 59
- Cloud Security 26
- CSPM 18
- Compliance 14
- Container Vulnerability 9
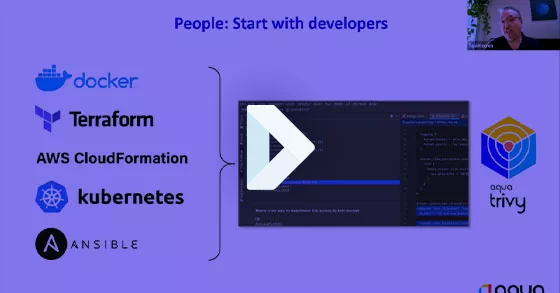
- DevOps and DevSecOps 18
- Docker Security 4
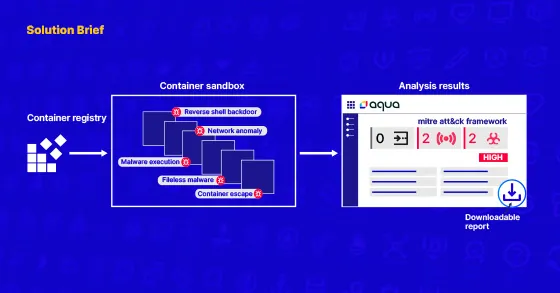
- Dynamic Container Analysis 5
- Google Cloud Security 9
- Image Vulnerability Scanning 11
- Kubernetes Security, KSPM 40
- Open Source 15
- Pivotal Cloud Foundry 3
- Red Hat OpenShift 10
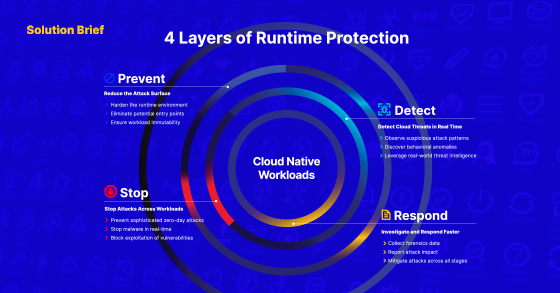
- Runtime Security 17
- Secrets Management 2
- Secure VMs 3
- Security Threats 18
- Serverless 9
- Service Mesh 2
- Vulnerability Management 13
- Show more
Types
- All
- Case Study 20
- eBook 11
- Infographic 2
- Research and Reports 24
- Solution Brief 26
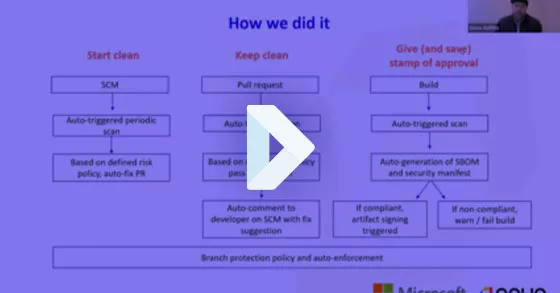
- Video 20
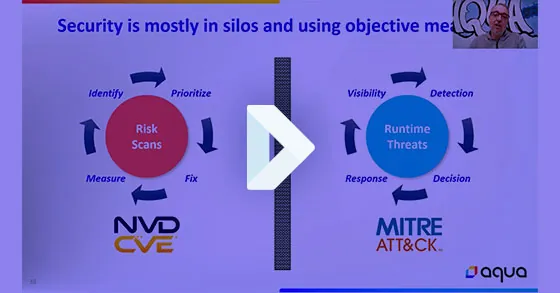
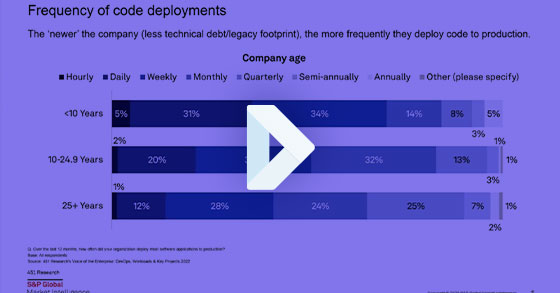
- Webinar 82
- Whitepaper 28
No matching resources for ""